The New Beat of Biometrics
There are mixed opinions about biometrics, despite being a mature technology in many ways. Projects of scope вҖ” from retail chains to government programs вҖ” have taken the media spotlight. As a result, failure and success stories alike make it difficult for the industry to issue a sound verdict.
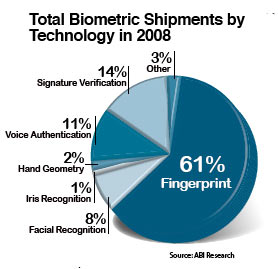
Despite skepticism, biometric shipments are growing. It is flourishing in government applications. India uses both fingerprint and facial recognition to screen individuals applying for national ID cards. In oil-rich regions like the Middle East, iris recognition is used to screen foreign workers, with the United Arab Emirates expelled 300,000 people in the last five years for illegal entry. The U.S., Japan and the U.K. currently use biometrics to screen foreign visitors for suspected terrorists or violators of immigration laws.
Unfortunately, it is not all smooth sailing. Failed projects include the high-profile and terminated Verified Identity Pass project in the US Verified Identity Pass, a provider of smart cards embedded with iris or fingerprint biometrics, recently operated at 20 US airports. Individuals would pay a fee, undergo a background check and receive expedited processing through security lines. However, government fear of terrorists with clean backgrounds exploiting the program prevented it from providing any benefit beyond a shorter line, and eventually the value of the service was diminished, said Walter Hamilton, Chairman of the International Biometric Industry Association and a Senior Consultant with Identification Technology Partners.

The fundamental problem with biometrics today is not so much the technology, but its real-life applications. Issues like being unable to fulfill its promised ROI must be addressed before implementation, along with ensuring privacy. It is perhaps more important for biometrics to deliver what is promised, and to protect and verify the identities of all involved.

Standardizing Testing Protocols
In security, established products are usually preferred to novel technologies, and biometrics is such a dynamic and research-intensive field that buyers are faced with products that have not had an ideal period of "settling in," said Stephen Wilson, MD of Lockstep Consulting.
If a biometric could be overcome by using spoofing techniques such as jelly fingers (fingerprint), or photographs and video (face recognition and iris), the potential losses and reputational damage could make it worthless as an authentication method, said Bill Reding, Information Security Consult ant of UK Payments. Additionally, minimizing false acceptances and false rejections is critical in ensuring security and customer acceptability. This makes accuracy a primary challenge and criterion of biometrics.
Biometrics testing involves a large number of different presentations of a body part, with measurements of false reject rate (FRR) and false acceptance rate (FAR), Wilson said. At present, there are few agreed standards for measuring and comparing biometrics performance.
False rejects frustrate users the most; they can raise system costs, lower productivity and cause match thresholds, resulting in lowered security, said Daniel Bailin, VP of Channel Sales at Lumidigm.

Technologies Gaining Momentum
With fingerprint recognition in the lead, facial, iris, vascular, voice, signature verification and DNA are other viable alternatives.
Facial Recognition
Improvements in accuracy have placed facial recognition among the fastest growing biometrics. It is the primary biometric required for e-passports that comply with the International Civil Aviation Organization standards, said RJ Langley, VP of Daon.
"It can be captured in a non-intrusive way, and is relatively easy to automate," said Dr. Joseph Atick, Executive VP and Chief Strategic Officer, L-1 Identity Solutions. Because there is an existing database of face images, recognition systems can locate duplicate enrollments and eliminate identity fraud.
The National Institute of Standards and Technology stated that government ID applications with video surveillance include facial or iris recognition analytics, that identification can be done from surveillance, known as stand-off techniques, said John Mears, Director of Biometrics Solutions, Information Systems and Global Services, Lockheed Martin.
Large-scale areas such as stadiums, railway stations, malls and so on also pair facial recognition with video surveillance, said Navin Rajendra, Senior Research Analyst of Frost & Sullivan.

In conflict zones like Iraq and Afghanistan, facial biometrics are collected and matched against a database for ID checks during employment or access to secured areas. "Our department anticipates biometrics being used more and more for business applications such as equipment issue, verification of job and language skill testing, and management of personnel during transportation," said Myra Gray, Director of the Biometrics Task Force, US Department of Defense.
Iris Recognition
Acquisition of templates and availability of databases are the two primary challenges of iris recognition. Though high in accuracy, acquisition is difficult to perform at a distance, and more complicated when the subject is uncooperative, Atick said. Also, few databases exist as a starting point, unlike facial recognition with available digital images, Hamilton pointed out.
Despite these problems, ABI Research estimates iris recognition will have high growth, comparable to facial recognition. Recent innovations now allow the iris to be captured from a distance of 2 to 3 meters.

Providers recognize commercial adoption requires changes. "We're shrinking capture devices to fit in the palm and providing a large-scale server that allows you to identify individuals in a population of millions or more," said Mohammed Murad, VP of Global Business Development and Sales, LG Iris.
For user friendliness, capture devices can allow an individual to take two pictures and store both credentials on the device or a server. Identities can be matched, in less than two seconds, against the server database via Wi-Fi, Murad said.
Vein scanners have been gaining traction in markets like Japan and Korea, Rajendra said. The emphasis on hygiene has been a driving force for the use of contactless biometrics.
"We expect the global annual growth of vein authentication to be 26 percent from 2009 to 2011," said Tatsuya Yoshida, Assistant Manager, Security and Smart ID Solutions Division, Hitachi. "In Japan, 80 percent of banks, which use biometric identifications, are now implementing finger vein authentication."
Apart from financial institutions, small-scale access control for equipment such as lockers can embed finger vein scanners for heightened protection. In Japan, retail transactions can be carried out with finger vein authentication, Hamilton said.
Voice Verification

Voice verification is proving valuable for enhanced call center interactions, banking and payment adoption, said Jonathan Collins, Principal Analyst, Short Range Wireless, ABI Research. Experts say the algorithms cope well with signal variability over different telephony equipment and networks, although temporary changes to the voice caused by colds and allergies can be problematic.
Integration and Interoperability
The International Organization for Standardization has grown to more than 50 standards that will provide the basis for development and integration of biometrics equipment over the next five years. "Integration remains a significant industry in itself, worth more than $1 billion last year alone," Collins said.
However, interoperability issues remain. Each basic trait, such as face or fingerprint, will generally have more than one possible algorithm, and algorithms do not usually interoperate, Wilson said.

Multimodal Technologies
Multimodal technologies combine two or three biometric modalities for improved accuracy and flexibility, Atick said.
It is happening at the US Department of Defense with its Automated Biometric Identification System database, and will soon be employed with the FBI's Next Generation Identification program. "We, therefore, believe the modalities of facial recognition and iris scans are the next in line for widespread adoption for identification of terrorists," Gray said.
Facial sees wide adoption as a supplement to fingerprint in low-end consumer applications. A camera embedded with facial recognition software can be added to a fingerprint system, with the resulting product perceived to be more convenient and secure than fingerprint alone, Bailin said.

